Overview of selected scams - April 2024
We present the report on identified threats and the methods of operation by criminals for the month of April 2024. This document highlights selected risks to customers of Polish banks. We encourage you to review the material. The document does not cover threats that have been known for many months and were described in an earlier report, such as the "classicscam", fake Facebook login panels, fake shops and other. It is essential to remember, however, that these scenarios are still being used by criminals, and we must continually work against them.
False investment schemess
A well-known but still very popular fraud scenario is fake investments. This scam involves cybercriminals impersonating famous people or institutions to entice potential victims to invest money with promises of high returns, only to cause significant financial losses.
Criminals continue to use deepfake technology to create fraudulent content. They use images of famous people to generate videos encouraging supposed investments. In April 2024, we noticed criminals overlaying videos with graphical modifications (Fig. 1). This may be an attempt to evade detection systems implemented on social media platforms.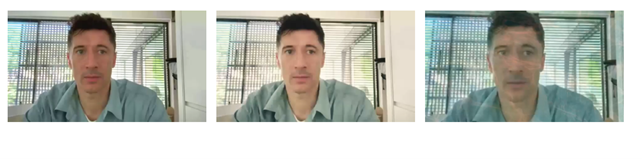
Figure 1 The use of deepfake technology to create deceptive content
Fake offers (both video and static ads) are distributed through Facebook ads (Fig. 2) and MSN ads (Fig. 3).

Figure 2 Fake investment - ads on the Facebook platform
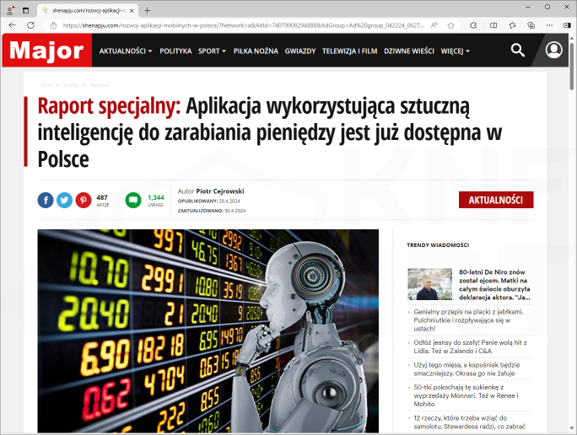
Figure 3 Fake investment - ads on MSN
Upon clicking on any of the links, the victim is directed to a page where they enter their contact information. Sometimes the data entry form is directly on Facebook (Fig. 4).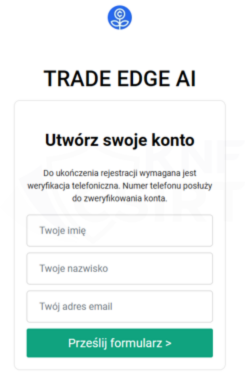
Figure 4 False investments - phishing site
The data obtained this way enables cybercriminals to contact the potentially already manipulated person and subsequently steal their funds. Many people still fall for this scenario, making it crucial to counteract it.
IMPERSONATING POLISH BANKS
Criminals use the image of well-known institutions to increase the credibility of phishing campaigns, regularly impersonating Polish banks. They use this method to steal electronic banking authentication data, payment card information, and encourage the download of malicious applications. In April 2024, this method remained in use.
Criminals, impersonating Polish banks, published ads on Facebook and sent iMessages (Apple’s messaging feature). Under the pretext of winning a prize, they stole electronic banking authentication data and payment card information.
Example Facebook Ads (Fig. 5):
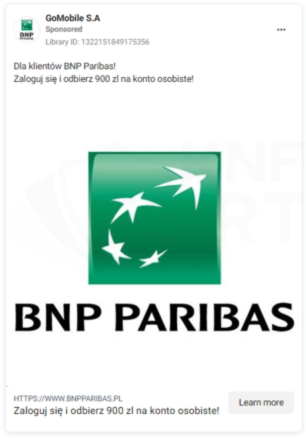



Figure 5 Ads impersonating polish banks
Example of iMessage impersonating Bank Peakos (Fig. 6):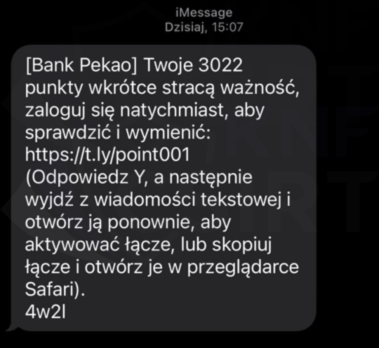
Figure 6 Fake iMessage - impersonating Bank Peako
Phishing sites (Fig. 7):
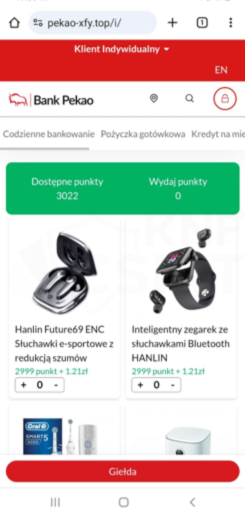
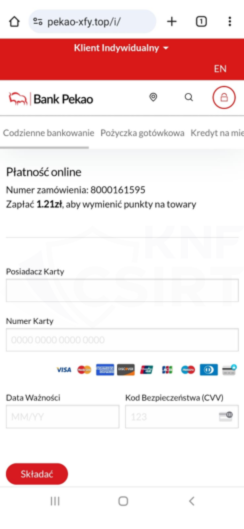
Figure 7 Phishing sites - impersonating Peako
INCOMPLETE ADRESSS - POLISH POST IMPERSONATION
Cybercriminals, impersonating Polish Post, informed about the need to update the address. They used iMessage (Apple’s messaging feature) to distribute the messages. A similar phishing campaign using Polish Post image occurred several times in 2023 and 2024.
Fake message (Fig. 8): 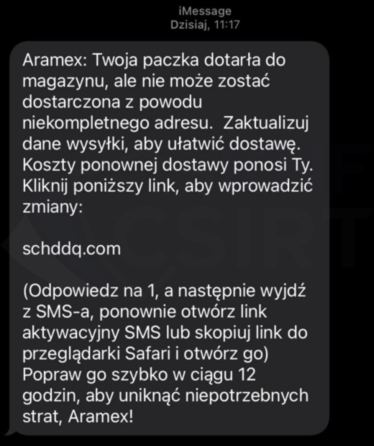
Figure 8 Fake iMessage - impersonating Post Polish
Phishing sites (Fig. 9):
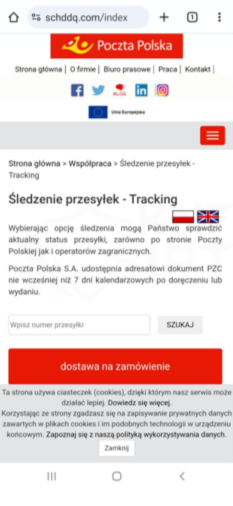
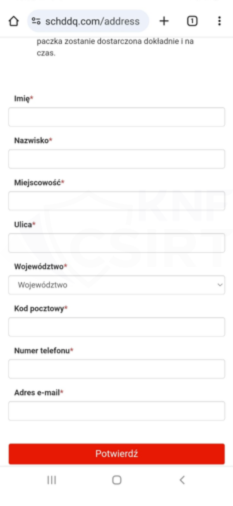
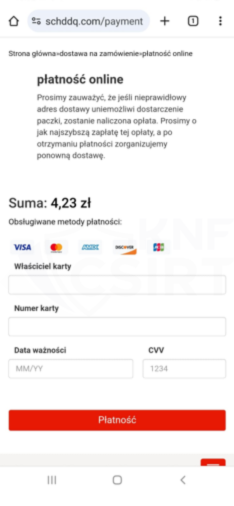
Figure 9 Phishing sites - impersonating Post Polish
CONFIRM ADRESS VIA LINK - INPOST IMPERSONATION
Criminals impersonated courier companies, this time using InPost’s image, informing about the need to complete the delivery address. They encouraged clicking a link leading to a phishing site to steal payment card information.
Fake SMS message (Fig. 10):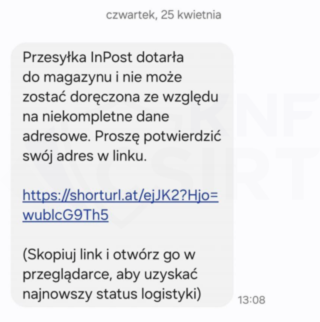
Figure 10 Fake SMS - impersonating InPost
Phishing sites (Fig. 11):
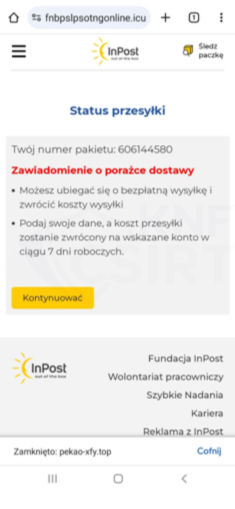
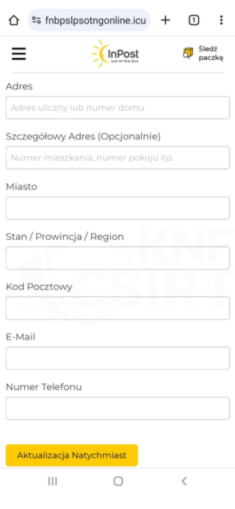
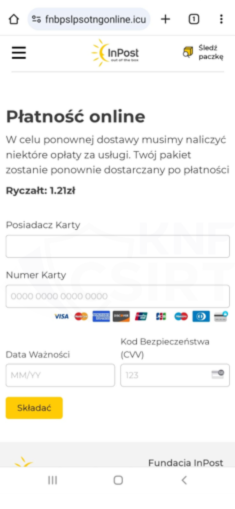
Figure 11 Phishing sites - umpersonating InPost
ACCOUNT SUSPENSION - ALLEGRO IMPERSONATING
Criminals prepared a phishing campaign informing about the alleged suspension of an Allegro account. To unblock the account, victims were prompted to update their transaction data by clicking "UPDATE YOUR DATA," leading to a phishing site to steal payment card information.
Fake e-mail message (Fig. 12):
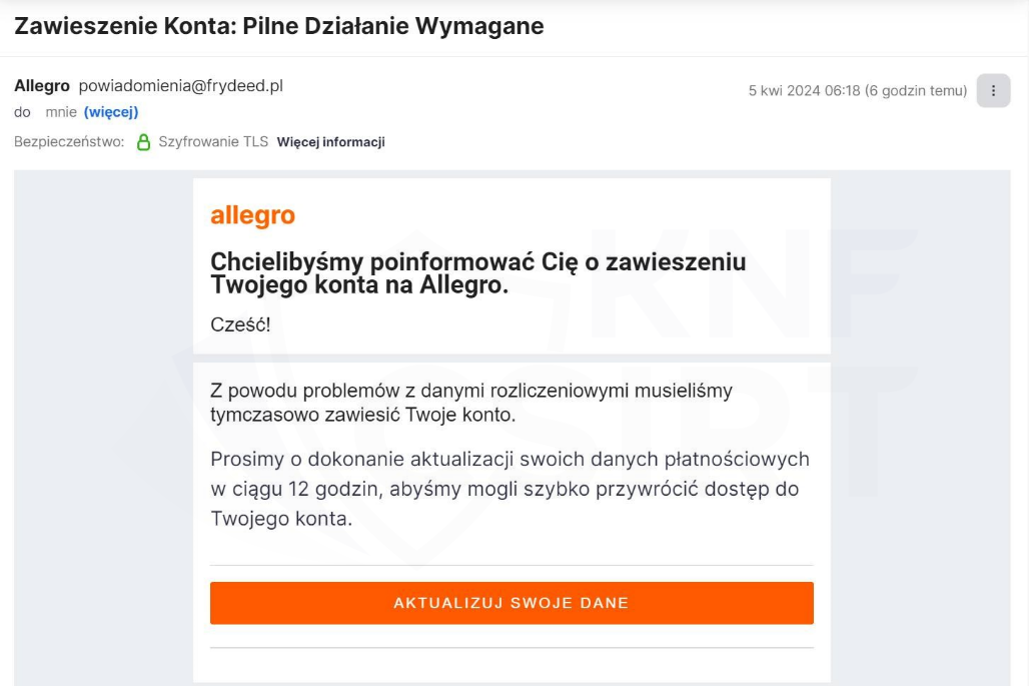
Figure 12 Fake e-mail message - impersonating Allegro
Phishing site (Fig. 13):
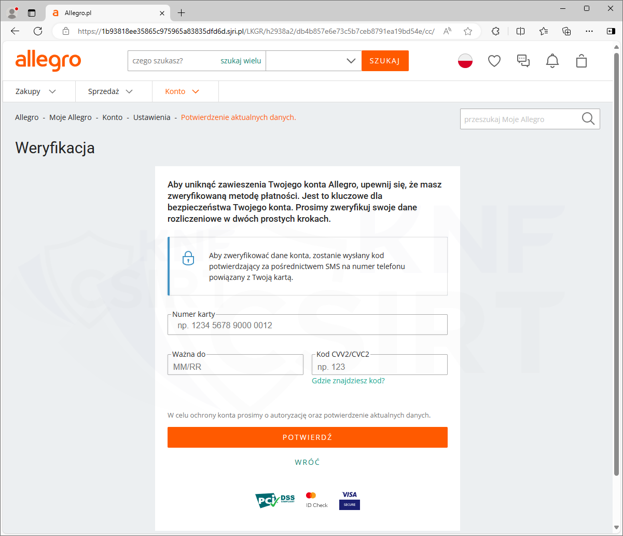
Figure 13 Phishing site - impersonating Allegro
NEW NFZ CARD VERSION - NATIONAL HEALTH FUND IMPERSONATION
Criminals prepared a phishing campaign informing about the possibility of getting a new NFZ card that "updates entitlements and ensures more effective health cost coverage." In reality, criminals stole payment card data and personal information.
Phishing sites (Fig. 14 - 15):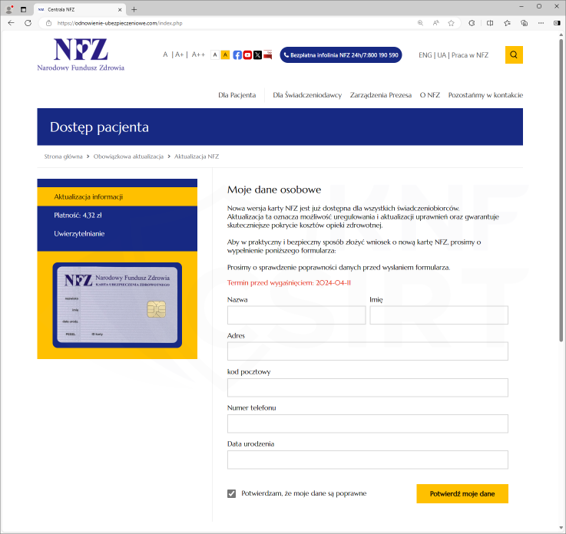
Figure 14 Phishing site - impersonating NFZ 1/2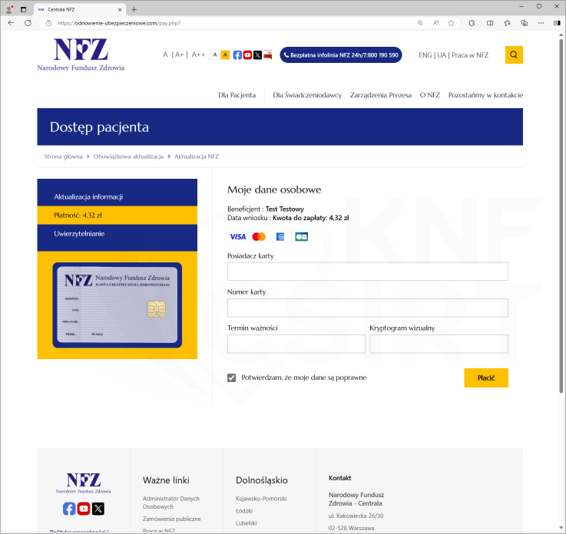
Figure 15 Phishing site - impersonating NFZ 2/2
VOD PLATFORM IMPERSONATION
In April 2024, criminals used the image of popular video platforms to steal payment card data and streaming account login credentials.
Fake e-mail message (Fig. 16):
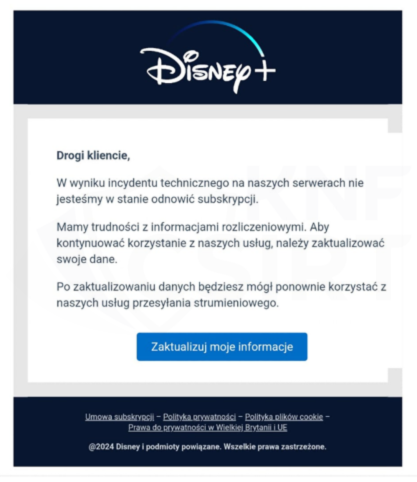
Figure 16 Fake email message - impersonating Disney+
Phishing sites (Fig. 17):
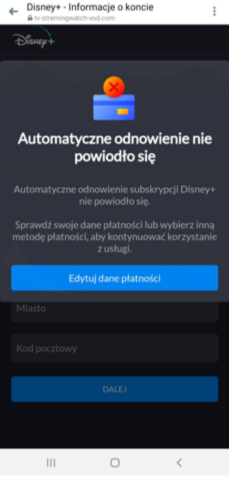
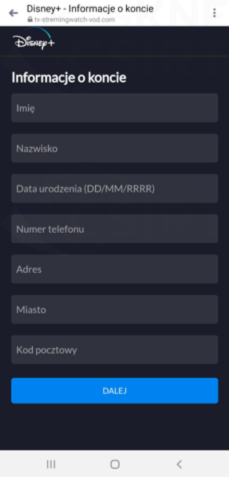
Figure 17 Phishing sites - impersonating Disney+
FREE FOR YOU - TEAM IMPERSONATION
Criminals again prepared a phishing campaign offering the possibility of getting the game Rust for free.
Fake Facebook Ads (Fig. 18):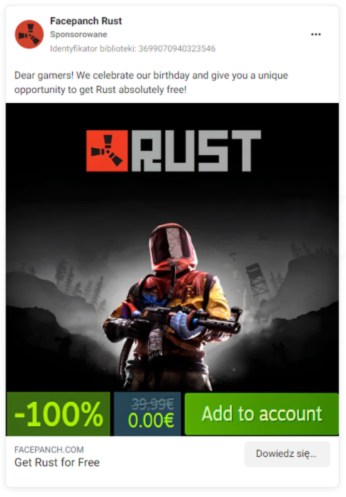
Figure 18 Ads offering a promotion for a game
Yet another month of this year has demonstrated that criminals are constantly refining their methods of operation. We consistently believe that conducting informational and educational activities is crucial.
That's why news about cyber threats and fraudulent trends are also published on the following our social media platform: Twitter, LinkedIn and Facebook.

