Overview of selected scams - June 2024
We present the report on identified threats and the methods of operation by criminals for the month of June 2024. This document highlights selected risks to customers of Polish banks. We encourage you to review the material. The document does not cover threats that have been known for many months and were described in an earlier report, such as the "classicscam", false invest, fake Facebook login panels, fake shops and other. It is essential to remember, however, that these scenarios are still being used by criminals, and we must continually work against them.
IMPERSONATING POLISH BANS
Criminals use the image of well-known institutions to increase the credibility of phishing campaigns, regularly impersonating Polish banks. They use this method to steal electronic banking authentication data, payment card information, and encourage the download of malicious applications. In June 2024, criminals continued to use this method, distributing phishing sites through social media ads and email messages.
FAKE FACEBOOK ADS AND EMAIL MESSAGES
Criminals impersonating Polish banks published ads on Facebook. They promised to award prizes and offer cashback for every purchase. In reality, they were phishing for online banking login credentials.
Example Facebook Ads (Fig. 1):


Figure 1 Ads impersonating Polish Banks
Example of an email messages impersonating Alior Bank ( Fig. 2):
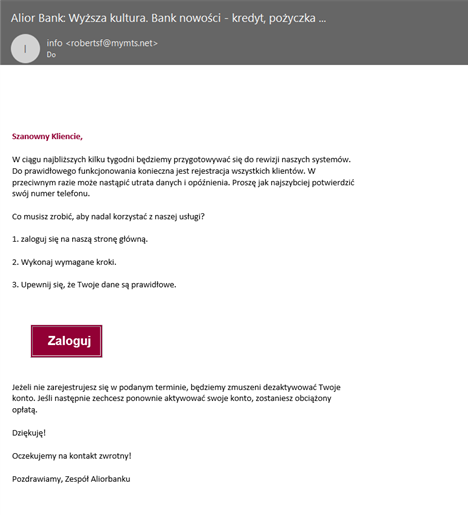
Figure 2 E-mail messages impersonating Polish Bank
Phishing sites (Fig. 3):
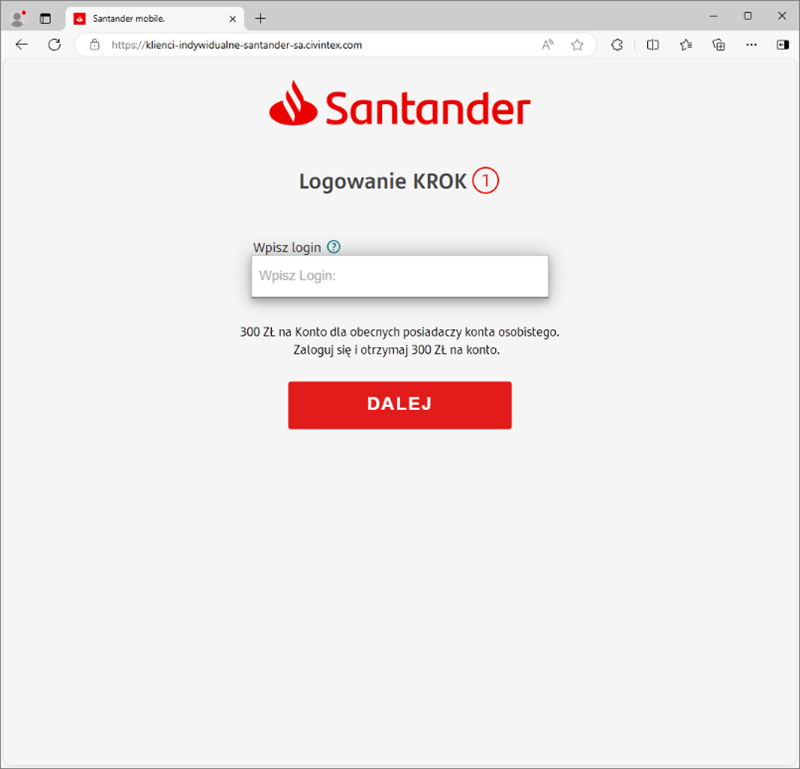
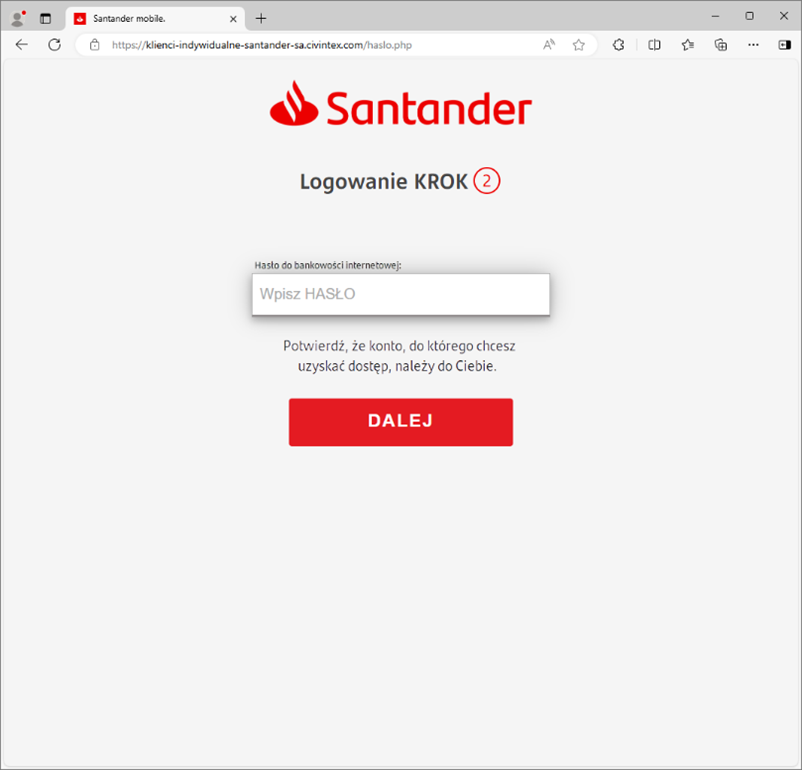
Figure3 Phishing sites - impersonating Santander Bank Poland
SYSTEM REVIEW, IMPERSONATING ALIOR BANK
Criminals were impersonating Alior Bank. They sent emails informing recipients about a system review and the necessity to update their data. The emails encouraged recipients to click on a link that led to a phishing site. This site mimicked the online banking login page.
Example e-mail message (Fig. 4):
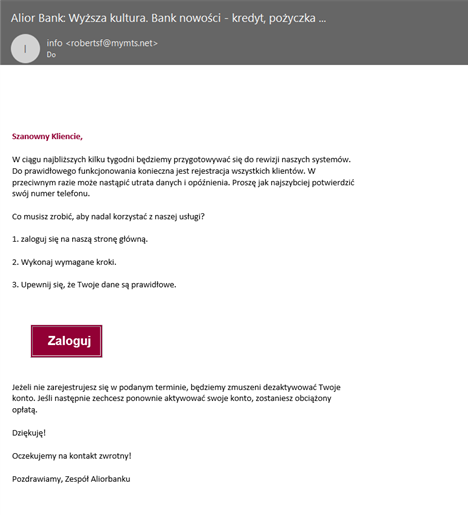
Figure 4 Fake e-mail message - impersonating Alior Bank
Phishing site (fig. 5):
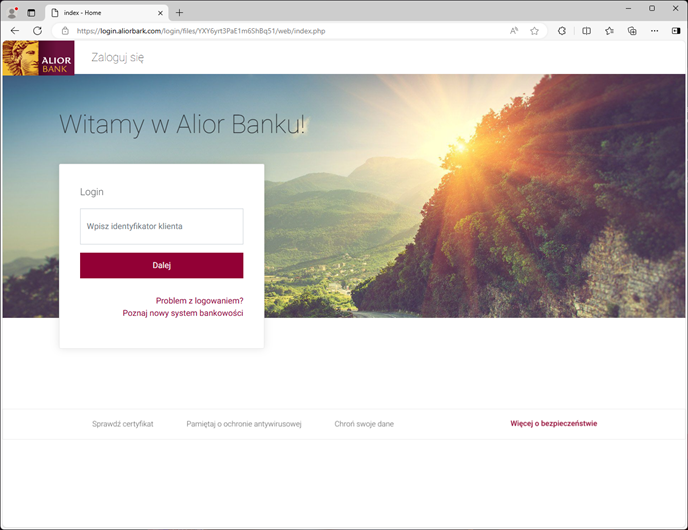
Figure 6 Phishing site - impersonating Bank Peako
IMPERSONATING PEKAO BANK
Criminals were impersonating Bank Pekao. They were phishing for online banking login credentials and payment card information, justifying this as necessary for security reasons and to verify the accuracy of data.
Phishin sites (Fig. 7-8):
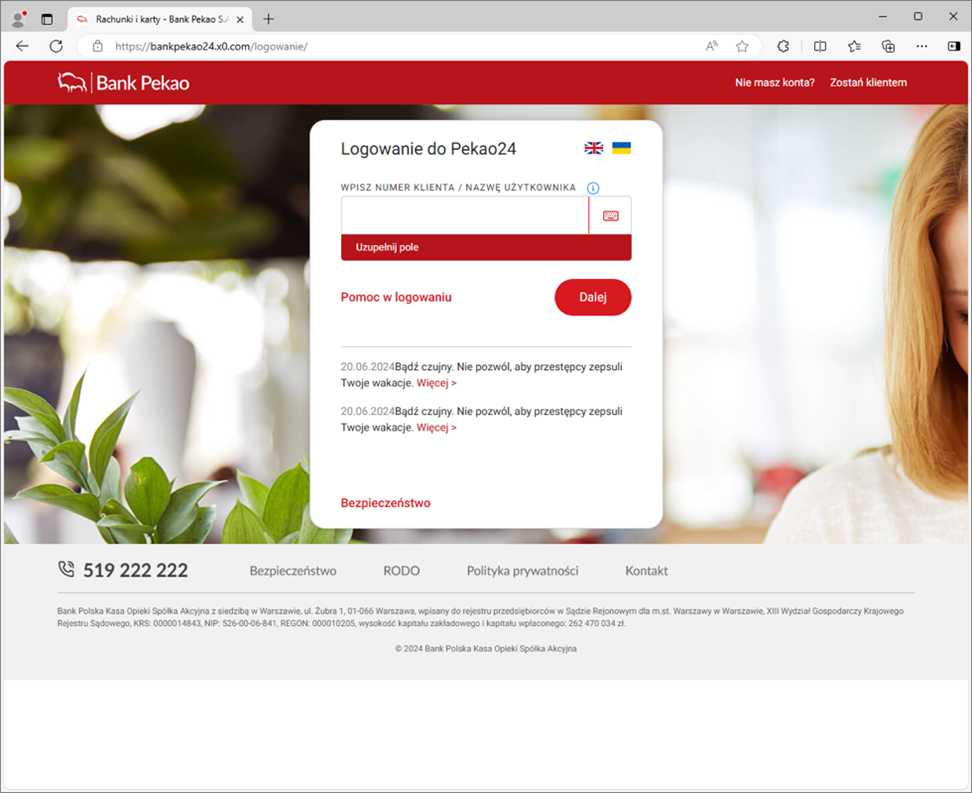
Figure 7 Phishing site - impersonating Pekao Bank 1/2
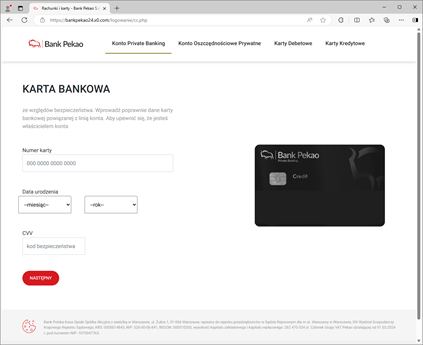
Figure 8 Phishing site - impersonating Pekao Bank 2/2
PRODUCTS AVAILABLE FOR PURCHASE FOR 9 PLN
Cybercriminals published ads on the Facebook platform informing about the alleged opportunity to purchase items at low prices. In reality, the website linked from the ad aimed to phish for payment card details. Sebsequently, the criminals attempted to commit fraud using a "subscription model".
Example Facebook Ads (Fig. 9-10):
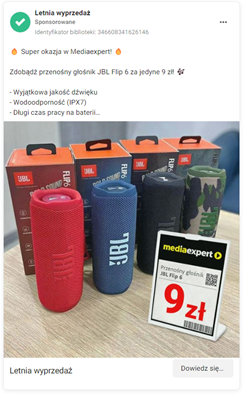

Figure 9 Fakes ads - sales for 9 PLN 1/2
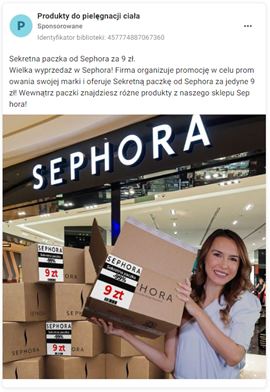
Figure 10 Fakes ads - sales for 9 PLN 2/2
SET OF CANS AND COCA-COLA REFRIGERATOR
Cybercriminals published ads on the Facebook platform, advertising the alleged opportunity to buy 24 cans of Coca-Cola and receive a refrigerator, all for only 9 PLN. In reality, the website linked in the ad was designed to phish for payment card details. Similar to the scenario described above, the criminals tried to withdraw funds from accounts using a "subscription model."
Example Facebook Ads (Fig. 11):

Figure 11 Fake ads - impersonating Coca-Cola
Phishing sites (fig. 12):
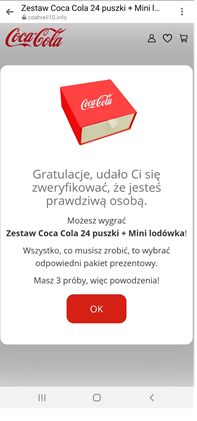
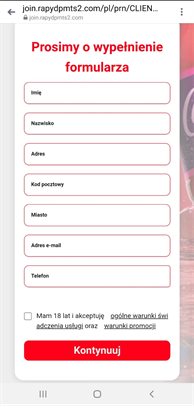
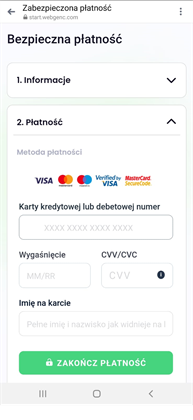
Figure 12 Phishing sites - impersonating Coca-Cola
‘FAST AND SECURE TOP-UP’, IMPERSONATING ORANGE
Cybercriminals were impersonating Orange. They created a website that purportedly allowed users to top up their prepaid phones and receive bonuses. In reality, it was a phishing site designed to harvest payment card details.
Phishing sites (Fig. 13-14):
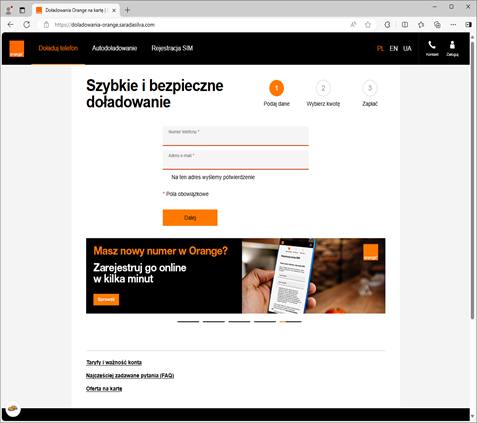
Figure 13 Phishing site - impersonating Orange 1/2
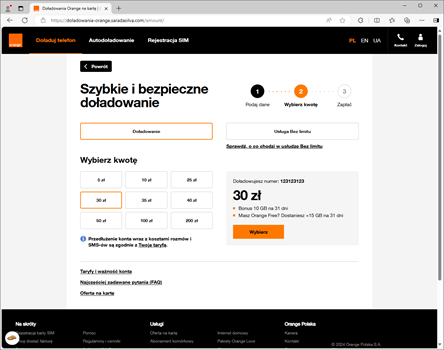
Figure 14 Phishing site - impersonating Orange 2/2
INCOMPLETE ADRESS – POLISH POST IMPERSONATION
Cybercriminals, impersonating Polish Post, informed about the need to update the address. A similar phishing campaign using Polish Post image occurred several times in 2023 and 2024.
Fake message (Fig. 15):
Figure 15 Fake sms message - impersonating Post Polish
Phishing sites (Fig. 16):
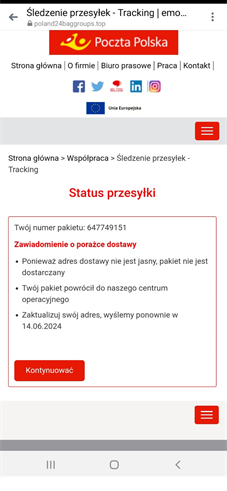
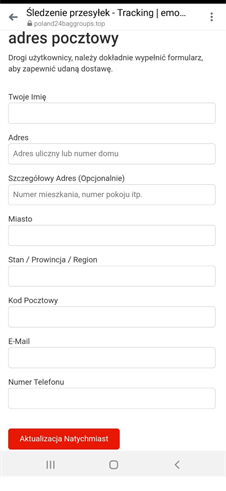
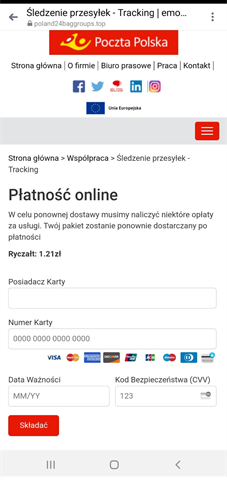
Figure 16 Phishing sites - impersonating Post Polish
CONFIRM ADRESS VIA LINK – INPOST IMPERSONATION
Criminals impersonated courier companies, this time using InPost’s image, informing about the need to complete the delivery address. They encouraged clicking a link leading to a phishing site to steal payment card information.
Fake SMS message (Fig. 17):
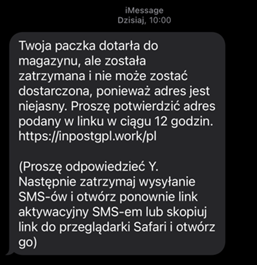
Figure 17 Fake SMS - impersonating InPost
Phishing site (Fig. 18)
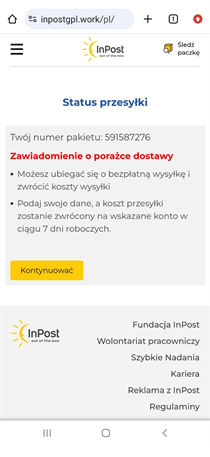

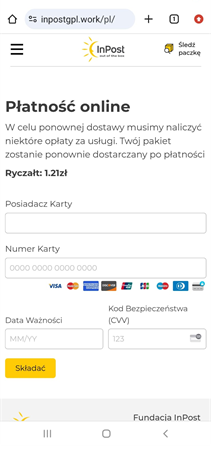
Figure 20 Phishing sites - impersonating InPost
Yet another month of this year has demonstrated that criminals are constantly refining their methods of operation. We consistently believe that conducting informational and educational activities is crucial.
That's why news about cyber threats and fraudulent trends are also published on the following our social media platform: Twitter, LinkedIn and Facebook.
