Overview of selected scams - November 2024

We present the report on identified threats and the methods of operation by criminals for the month of November 2024. This document highlights selected risks to customers of Polish banks. We encourage you to review the material.
The document does not cover threats that have been known for many months and were described in an earlier report, such as the "classicscam", phishing schemes posing as streaming platforms and other. It is essential to remember, however, that these scenarios are still being used by criminals, and we must continually work against them.
FALSE INVESTMENT SCHEMESS
A well-known but still very popular fraud scenario is fake investments. This scam involves cybercriminals impersonating famous people or institutions to entice potential victims to invest money with promises of high returns, only to cause significant financial losses.
Additionally, in November 2024, CSIRT KNF analysts also reported 218 fake profiles that posted fake investment ads for blocking (fig. 1).
Figure 1 Fake investment ads distributed on the Facebook platform
After clicking the link in the advertisement, the victim was directed to a website where the criminals attempted to obtain their contact information fraudulently (Fig. 2)
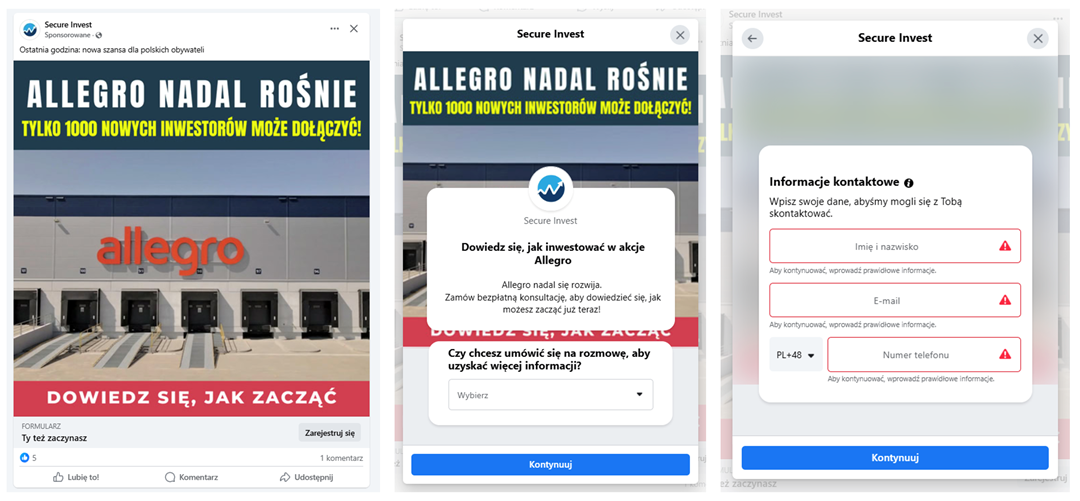
Figure 2 Fake Invest - contact data phishing pages
It is worth noting that in November 2024 again, most of the detected ads pertained to the second stage of the described scheme. In this stage, the criminals deceive individuals who were previously scammed, under the pretense of a supposed opportunity to recover the money they had initially lost. In reality, this is another attempt to defraud individuals who have already fallen victim to this scenario once before (fig. 3).
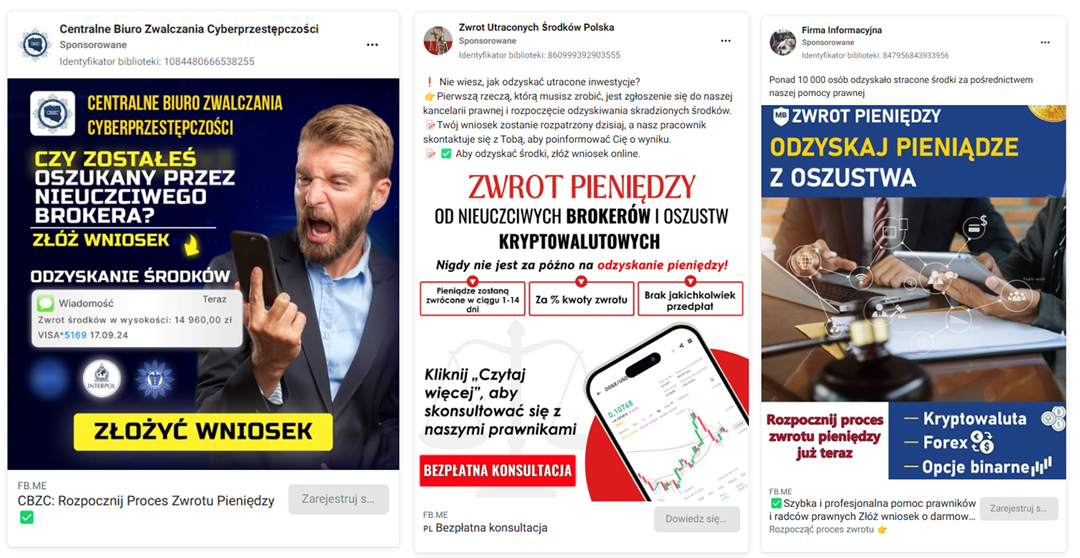
Figure 3 Fake invest - second stage of the described scheme
In the described scheme, the attackers continue to use deepfake recordings and fake applications. These do not infect devices but are designed to enhance the credibility of the content they present (fig. 4).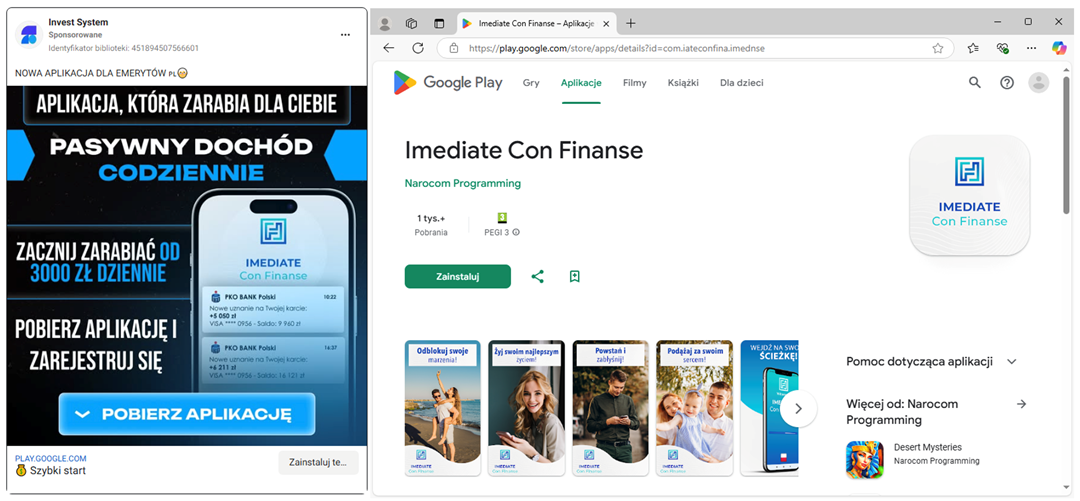
Figure 4 Fake invest - use of mobile app
CRIMINALS CAMPAIGN IN POLAND
In this section of the report, we present the identified criminal campaigns that directly impersonated organizations within the Polish financial sector and other organizations. Their aim was to steal personal information and banking product data.
"YOUR BANKING IS EXPIRING" - SCAM SMS MESSAGES
November 2024 was yet another month during which cybercriminals exploited the image of Polish banks to enhance the credibility of phishing campaigns. The attackers impersonated Bank Peako and Santander Bank Polska by sending SMS messages claiming that access to online banking was allegedly about to expire. To avoid inconvenience, recipients were urged to click on a link included in the message. In reality, the link led to a phishing website, closely resembling the legitimate one, aimed at stealing login credentials for online banking.
Example SMS messages and phishing sites (fig. 5-6):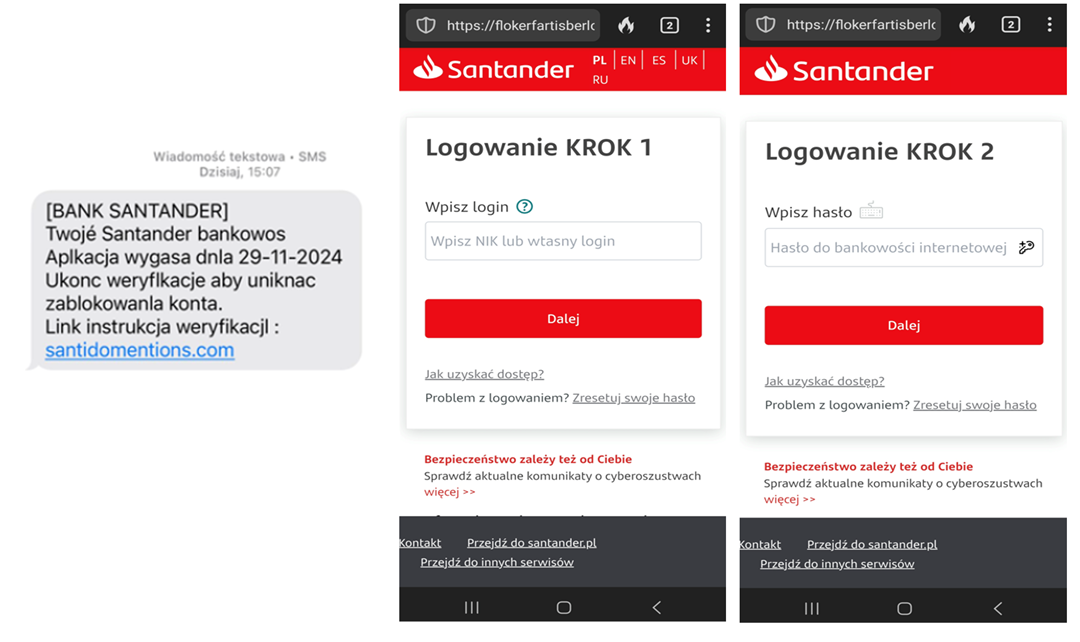
Figure 5 Bank impersonation - SMS messages and phishing sites 1/2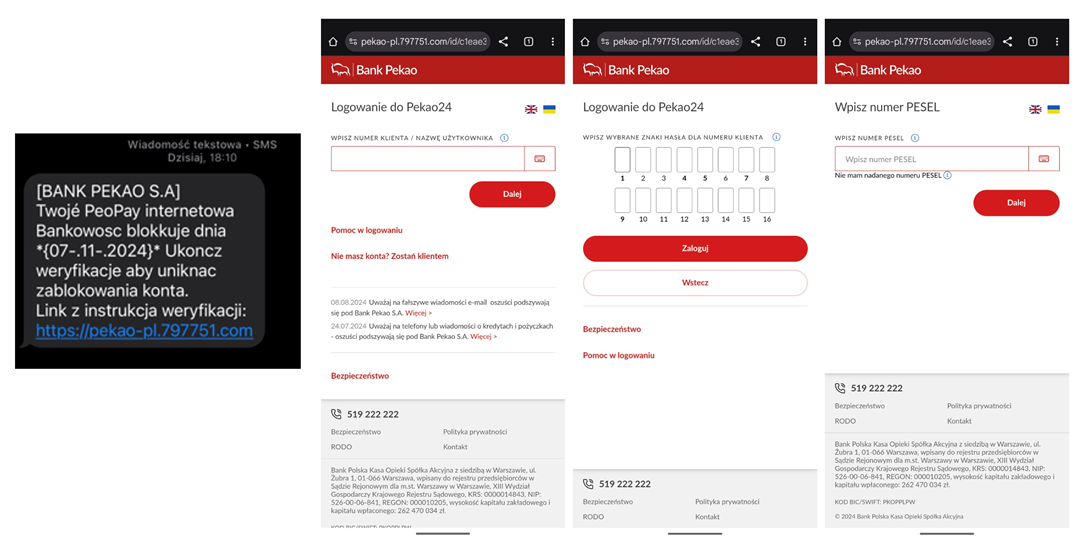
Figure 6 Bank impersonation - SMS messages and phishing sites 2/2
'CLAIM 500 PLN' - IMPERSONATION OF CREDIT AGRICOLE
Another campaign from the past month, in which cybercriminals exploited the image of a Polish bank, involved impersonating Credit Agricole. Under the pretext of completing a survey, for which victims were allegedly promised financial compensation, the attackers stole login credentials for online banking.
Example SMS messages and phishing sites (fig. 7):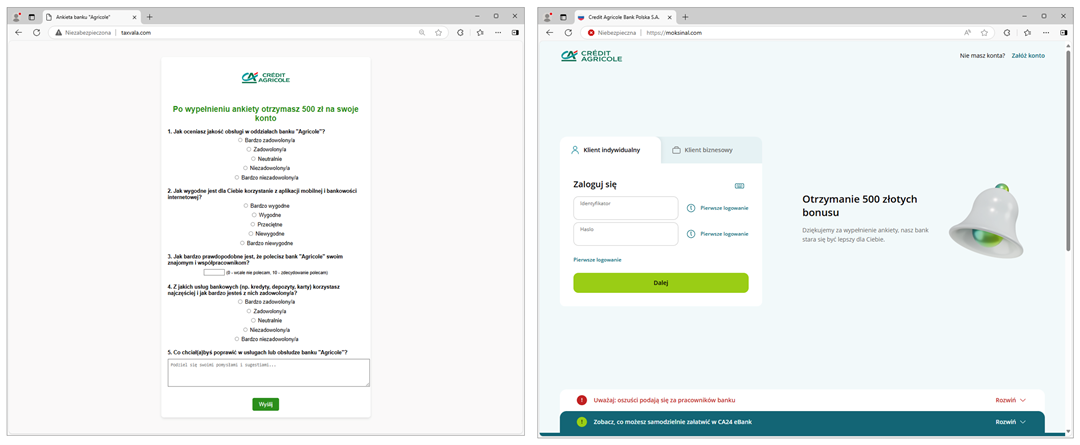
Figure 7 Impersonation of a Bank - Survey and Login Page
'A UNIQUE OPPORTUNITY' A LOST PACKAGE FOR 9 PLN
Once again, cybercriminals attempted to siphon funds from accounts using a "subscription model." This time, they published ads on the Facebook platform, claiming that users could purchase an unclaimed package for only 9 PLN (fig. 8).
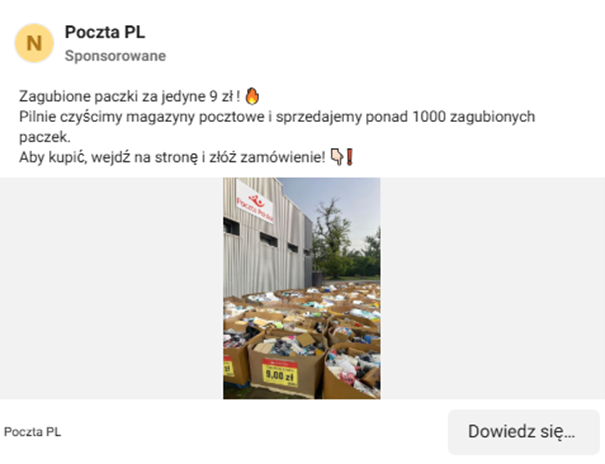
Figure 8 Fake ad - lost package
If someone fell for the scam and clicked on the link, they were redirected to a website where they were asked to answer a few questions (fig. 9).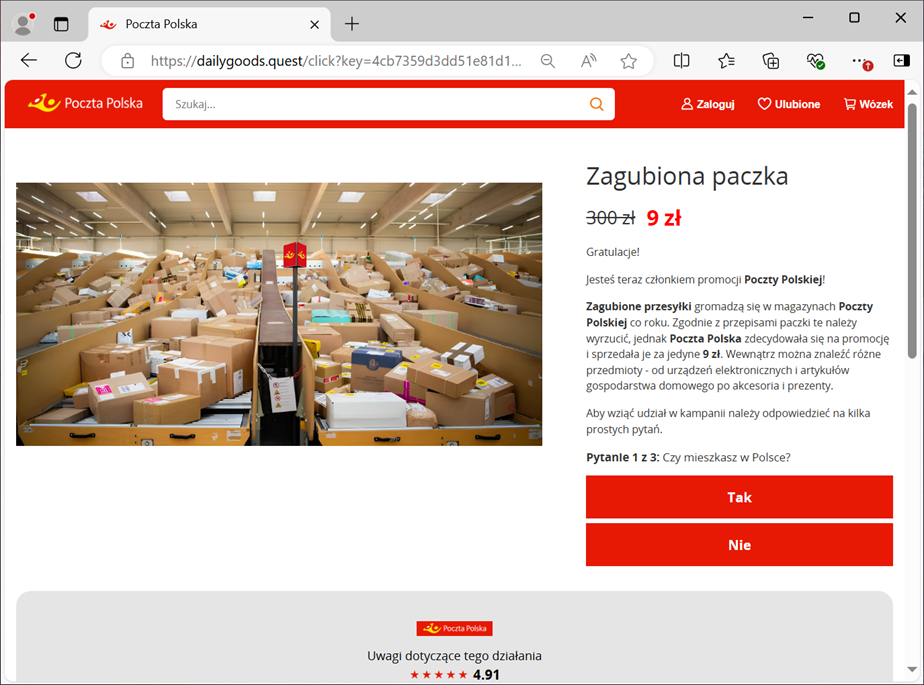
Figure 9 Adwersing questions - package for 9 PLN
Next, a form appeared prompting the user to enter their personal information and payment card details (fig. 10).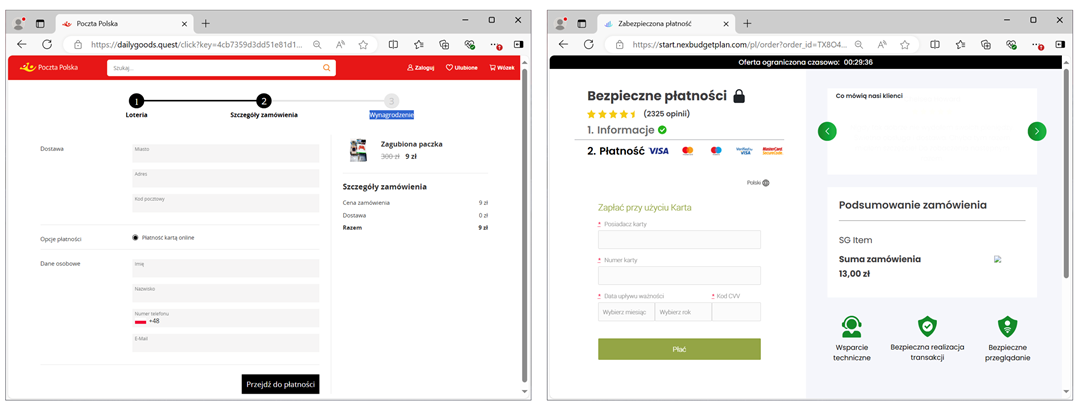
Figure 10 A form designed to steal personal information and payment card details
FAKE SHOPS - BLACK FRIDAY
Taking advantage of the busy shopping season, cybercriminals created fake stores, impersonating well-known brands. They distributed information about these stores through social media ads, enticing users with sales and promotions. In reality, the goal was to steal payment card details.
With the upcoming holidays, it is expected that such phishing campaigns will be employed by attackers more frequently than before.
Example fake ad and phishing site (fig. 11-12):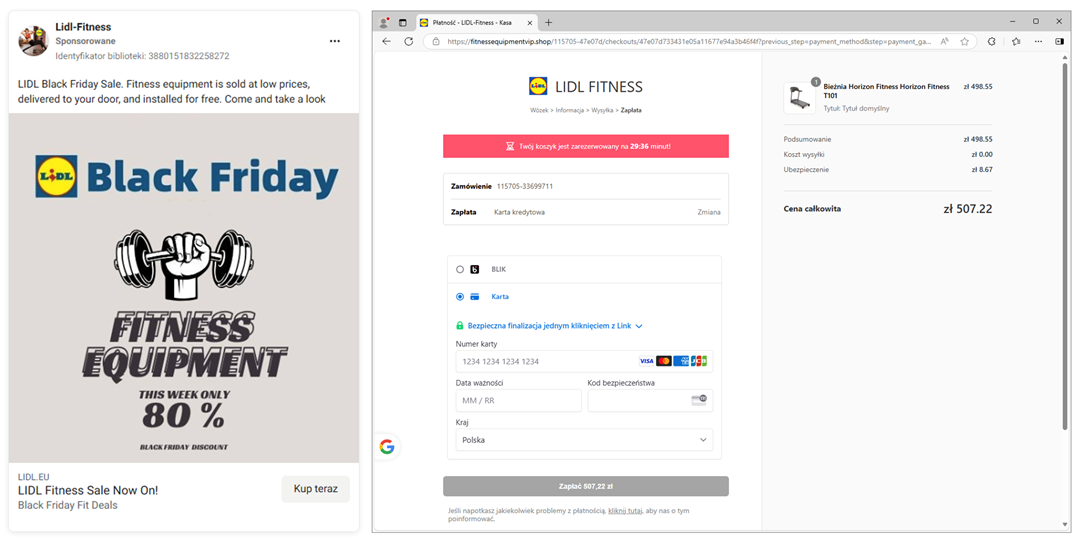
Figure 11 Fake shop - payment card information 1/2
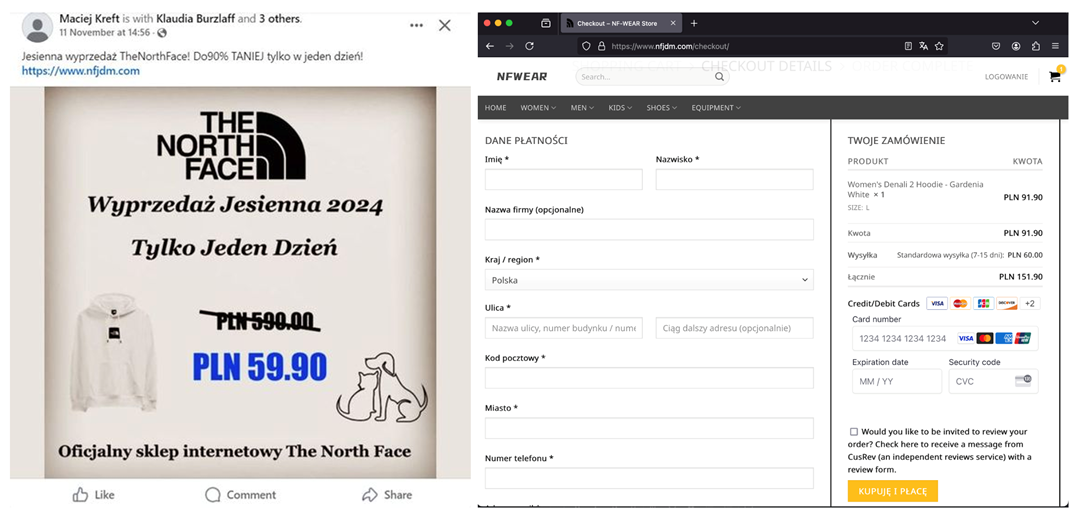
Figure 12 Fake shop - payment card information 1/2
QR CODES ON PARKING METERS IN KATOWICE
As reported on the "City of Katowice" profile on platform X (https://x.com/miasto_katowice), on November 20, 2024, stickers with QR codes were found on local parking meters. Scanning the QR code led to a website designed to steal personal data (fig. 13).
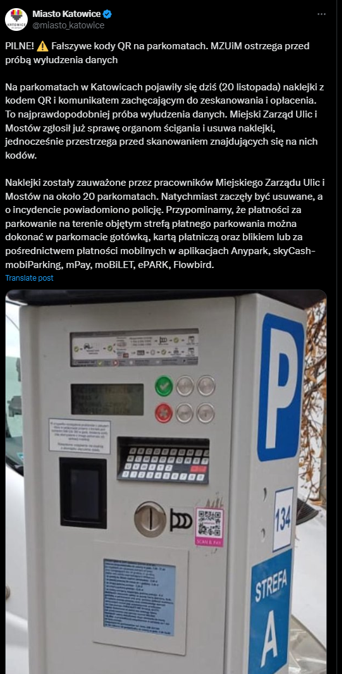
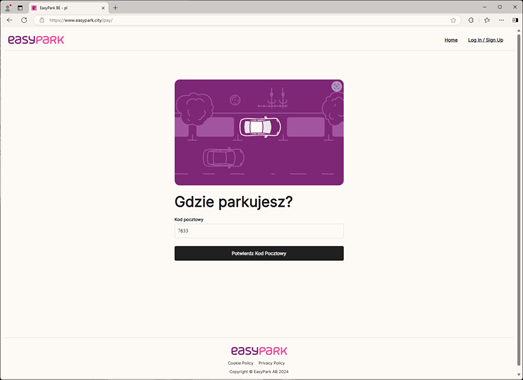
Figure 13 Notice about QR codes found on parking meters and the target website after scanning
We have encountered criminal campaigns distributing malicious QR codes through physical means before. This indicates that cybercriminals are relentless in devising new scenarios and schemes, as well as innovative methods for distributing harmful content.
That's why news about cyber threats and fraudulent trends are also published on the following our social media platform: Twitter, LinkedIn and Facebook.
